Apple is introducing a new cryptographic protocol for iMessage that is designed to protect users from sophisticated attacks using quantum computers. The new encryption protocol could safeguard users from scenarios where encrypted data has been stored, only to be decrypted using a quantum computer at a later date. iMessage is the second messaging platform known to introduce support for quantum-security cryptography — Signal’s PQXDH protocol was introduced last year — while adding another layer of security to protect users if keys are compromised.
The company detailed the development of the new PQ3 protocol for iMessage on Wednesday, ahead of its deployment on supported iPhone, iPad, Mac, and Apple Watch models. PQ3 is a quantum-resistant cryptographic protocol designed to protect conversations from being compromised by attackers with quantum computers in the future, according to Apple.
Traditional public key cryptography — used in secure messaging services like WhatsApp, iMessage, and Signal — protect users from powerful computers using difficult mathematical problems. However, powerful quantum computers are said to be capable of solving these problems, which means that even though they don’t currently exist, they can be used to compromise encrypted chats in the future.
Apple also highlights another challenge posed by quantum computers — the “Harvest Now, Decrypt Later” scenario. By storing vast amounts of encrypted data available today, capable attackers can gain access to the data at some point in the future once a powerful enough quantum computer is capable of breaking the traditional encryption used to protect those messages.
![]()
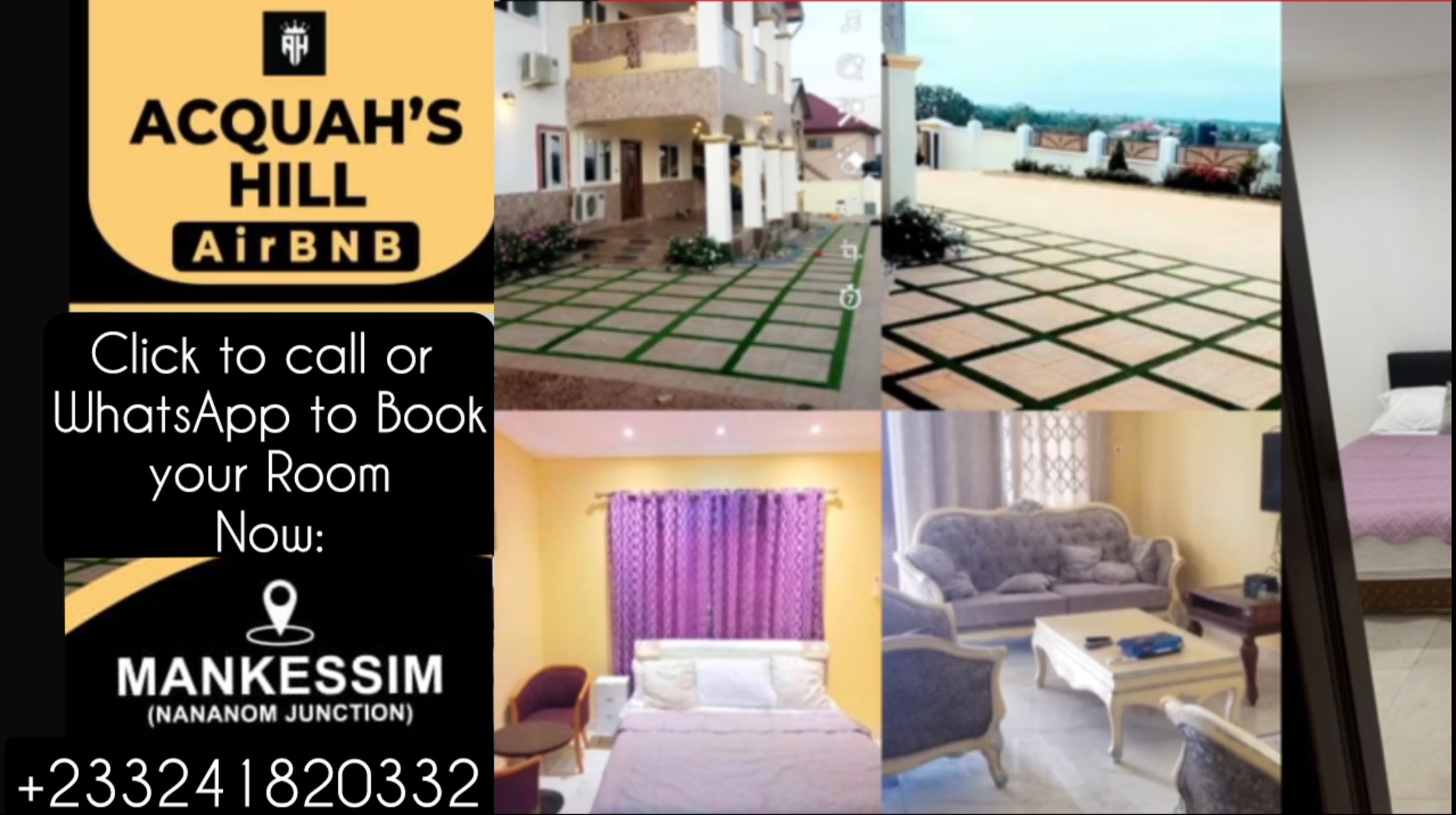
iMessage will join Signal in using quantum-resistant cryptography
Photo Credit: Apple
iMessage is the second messaging platform to add support for quantum-security cryptography. Last year, Signal — widely considered the gold standard in encrypted messaging — announced it was rolling out a new PQXDH protocol that would protect users from quantum computers. Apple says that its PQ3 encryption protocol goes one step further than PQXDH by changing post-quantum keys on an ongoing basis — this limits the number of messages that can be exposed if the keys are compromised.
The new PQ3 post-quantum encryption protocol is designed to protect users from existing and future adversaries and will be introduced from the start of a chat, according to Apple. It would need to be combined with the company’s existing encryption, with a hybrid design that means attackers would need to defeat both the traditional encryption and the post-quantum primitives used to protect iMessage conversations.
In order to protect users in case an encryption key is compromised, Apple says that a new post-quantum key is transmitted periodically (instead of with every message), to keep the size of these encrypted messages in check, while allowing users to access the service even in poor network conditions.
The new PQ3 protocol has been reviewed by the company’s Security Engineering and Architecture (SEAR) teams. It has also been reviewed by a team led by Professor David Basin, head of the Information Security Group at ETH Zürich, as well as Professor Douglas Stebila from the University of Waterloo. The company also says that it also contracted a third-party security consultancy independently assessed the PQ3 source code, and found no security issues, according to the company.
Apple says that the upcoming updates to iOS 17.4, iPadOS 17.4, macOS 14.4, and watchOS 10.4 will bring support for PQ3, and iMessage conversations on supported devices will automatically start to use the new quantum-security protocol to encrypt messages sent and received on the platform. All supported conversations will be upgraded to the post-quantum encryption protocol this year, according to the company.









![Mr Logic signs two dancehall artistes unto his Red Panther record label [Video]](https://ghananewss.com/storage/2023/05/Mr-Logic-signs--100x75.jpeg)






